In the ever-expanding digital universe, our personal, financial, and business information is constantly transmitted over the internet. This is where cryptography becomes our digital shield, protecting our information from prying eyes. But what exactly is cryptography, and how does it work? Let’s break it down into simpler terms.
What is Cryptography?
Imagine you have a secret message that you only want your friend to read. You write it in a code that only you and your friend understand. If anyone else finds the message, they’ll just see a jumble of nonsense. That’s what cryptography does with your digital information. It scrambles it so only the intended recipient can unscramble and read it.
Two Types of Secret Codes: Symmetric and Asymmetric
Cryptography uses two main types of secret codes: symmetric and asymmetric. Both types do the same basic job—protecting information—but they do it in different ways.
Symmetric Encryption: One Secret Key
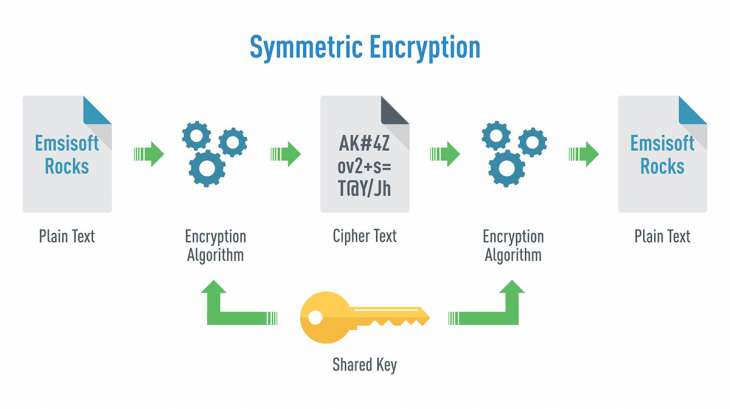
Symmetric encryption is like a locked notebook that you and your friend have one key to open. This single key locks (encrypts) and unlocks (decrypts) the notebook.
Stream Ciphers (A Type of Symmetric Encryption)
Stream ciphers work like a combination lock on a notebook, changing the combination for every entry you make. Each bit or byte of your message is encrypted one at a time, which is great for things like live video streaming, where the information keeps flowing.
Block Ciphers (Another Type of Symmetric Encryption)
Block ciphers are like making secret codes in blocks or chunks. Imagine you write your notebook entries in fixed-size blocks—say, 16 words at a time—and scramble each block with the key.
Real-Life Example of Block Cipher:
When you save a document on your computer, and it asks if you want to “encrypt” it, it’s often using a block cipher called AES (Advanced Encryption Standard) to scramble the information so only someone with the correct key can read it.
Asymmetric Encryption: Two Different Keys
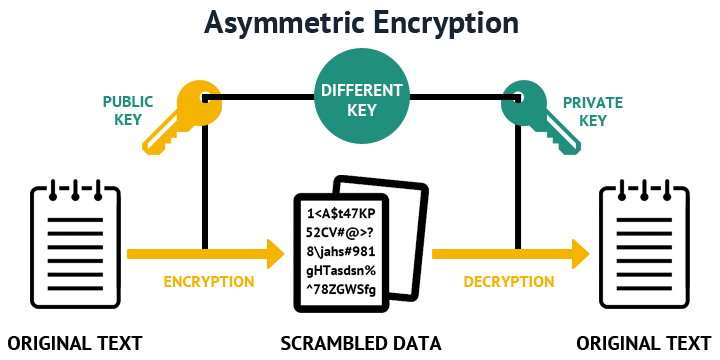
Asymmetric encryption uses two different keys: one public and one private. It’s like having a notebook with two locks. The public lock can be opened by anyone (the public key), but whatever is locked inside can only be unlocked by your own private key.
Real-Life Example of Asymmetric Encryption:
When you visit a secure website (look for “https” in the URL), the site gives your browser a public key to lock your information. Only the website has the private key to unlock it, keeping the information safe between you and the site.
Combining Both for Enhanced Security
In practice, the two types of encryption are often used together for better security. Here’s how it works:
- You start a secure session (like shopping online).
- The website uses asymmetric encryption to safely send you a symmetric “session key”—a temporary secret key just for this session.
- Your browser and the website switch to using this session key to scramble (encrypt) and unscramble (decrypt) everything you send and receive.
This way, they use the simpler symmetric key for the heavy lifting without the risk of someone intercepting the key.
Digital Signatures: Proving the Message is Yours
Digital signatures are like sealing wax on a letter. They prove that a message or document really came from you and wasn’t tampered with along the way. Here’s how a digital signature works:
- You “sign” a message with your private key, which can only be unlocked by your matching public key.
- You send your message out into the world.
- Anyone can use your public key to check that the message was really signed by you and hasn’t been changed since you signed it.
Digital signatures make sure that when you receive an email or download a file, it’s exactly what the sender intended, and it hasn’t been messed with on its way to you.
Conclusion: Cryptography Keeps Your Digital Secrets Safe
Cryptography, with its symmetric and asymmetric keys, session keys, and digital signatures, is the silent guardian of the digital world. It works behind the scenes every time you make a transaction online, send an email, or even just browse the internet, keeping your information safe and sound. By understanding these basics, you’re better equipped to appreciate the security measures that protect your digital life. Remember, whenever you’re online, cryptography is your invisible armor in the battlefield of cyberspace.